Sovereign infrastructure architecture
The operating layer beneath SAFI’s financial rails.
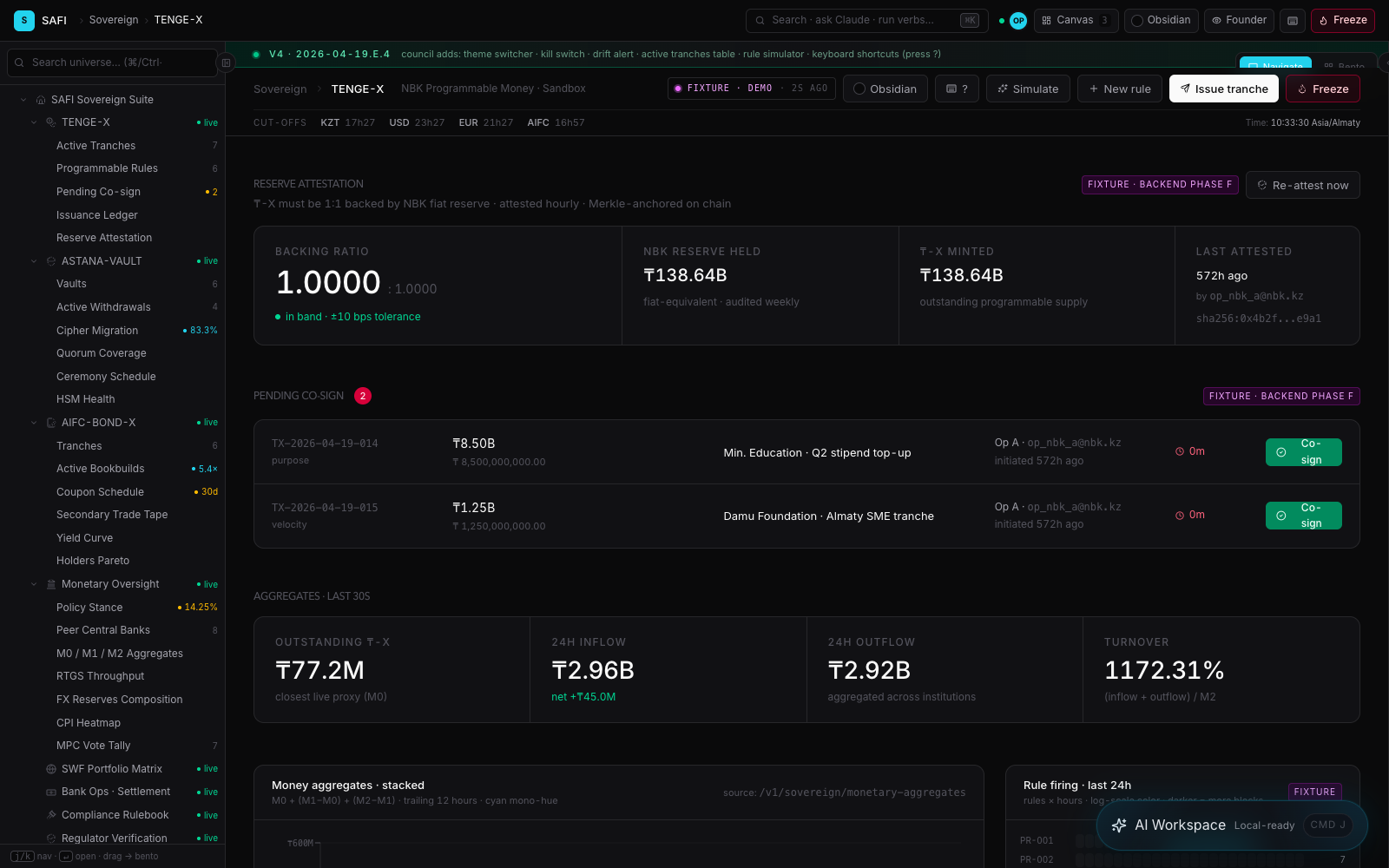
SAFI is built around an institutional trust spine: policy decisions, signed evidence, portable verification, custody controls, data-residency boundaries, programmable settlement logic, and audit-ready proof packages. The architecture is designed so governments, banks, custodians, venues, and capital partners can control high-value financial workflows without losing traceability, governance, or institutional review.
Sovereign rail explorer
SAFI is a system of control rails, not a single dashboard.
Select a rail to see the buyer workflow, control path, evidence artifact, and public-safe boundary. The goal is to show how the architecture turns high-value financial activity into inspectable operating evidence.
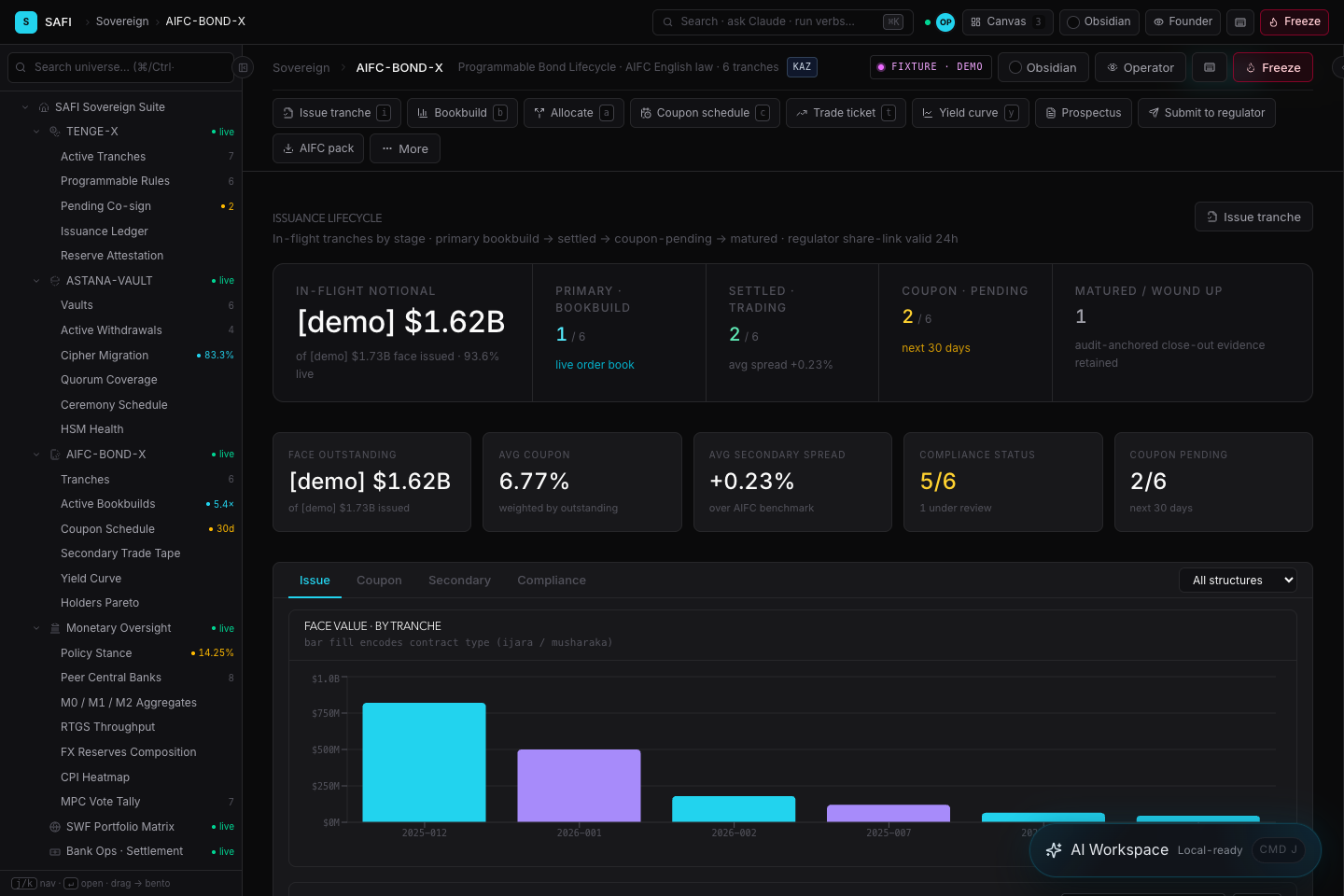
Real-asset lifecycle control
Issuers, trustees, banks, and capital partners need one controlled path for asset evidence, investor eligibility, transfer rules, servicing events, and investor reporting.
Layer map
SAFI is easiest to diligence as six layers, not as a single monolith.
Partner Workflow
Banks, issuers, custodians, trustees, Sharia boards, transfer agents, and regulated operators define the actual operating mandate.
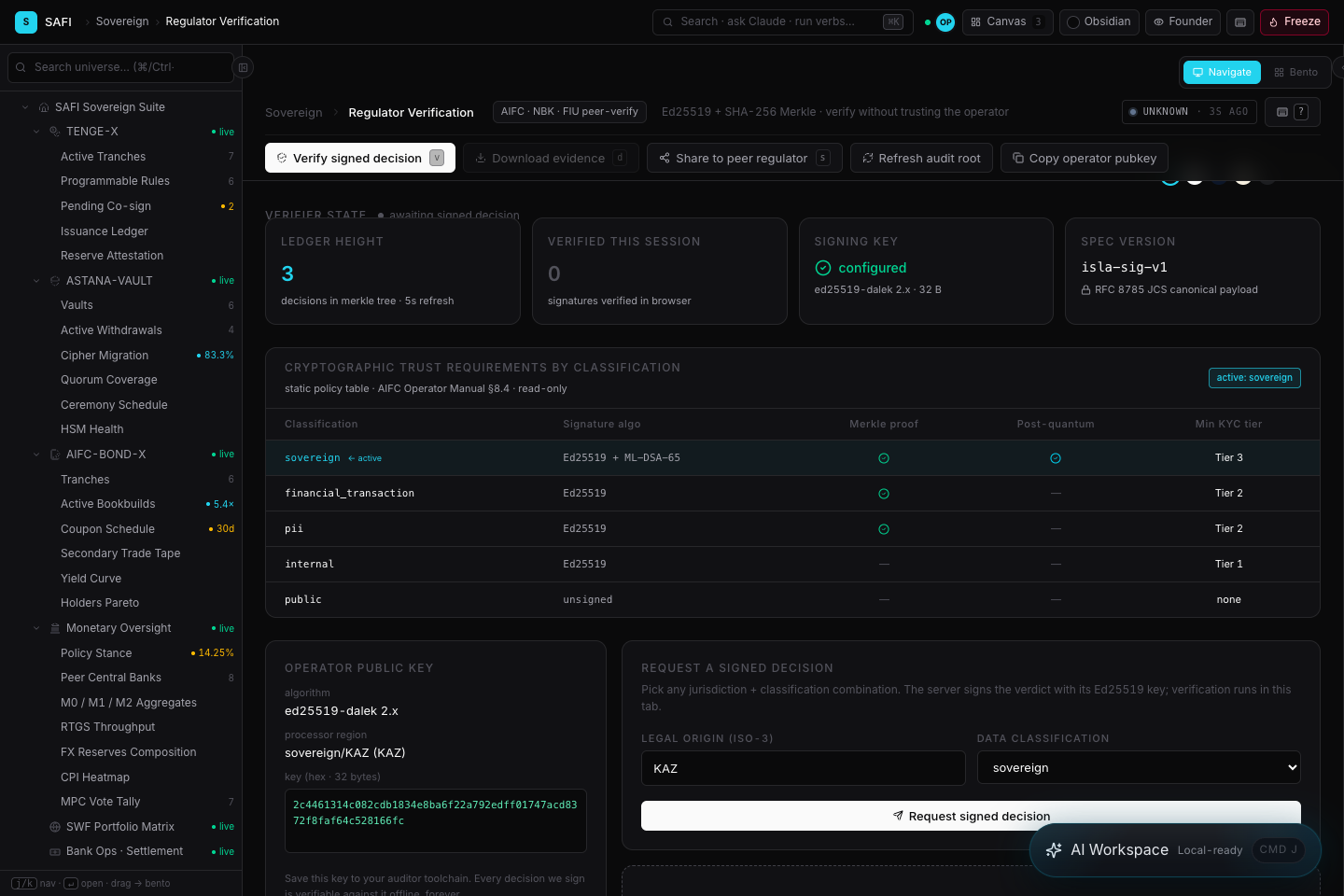
Blockchain 2.0 + Core Evidence Fabric
Financial evidence substrate, signed decisions, proof bundles, audit roots, reviewer exports, validator operations, and portable verification paths.
Control Rails
Capital Markets, VERIFY / PROOF, Vault Control, Money Rail, PAYAGENT Controls, and Islamic Finance Operations.
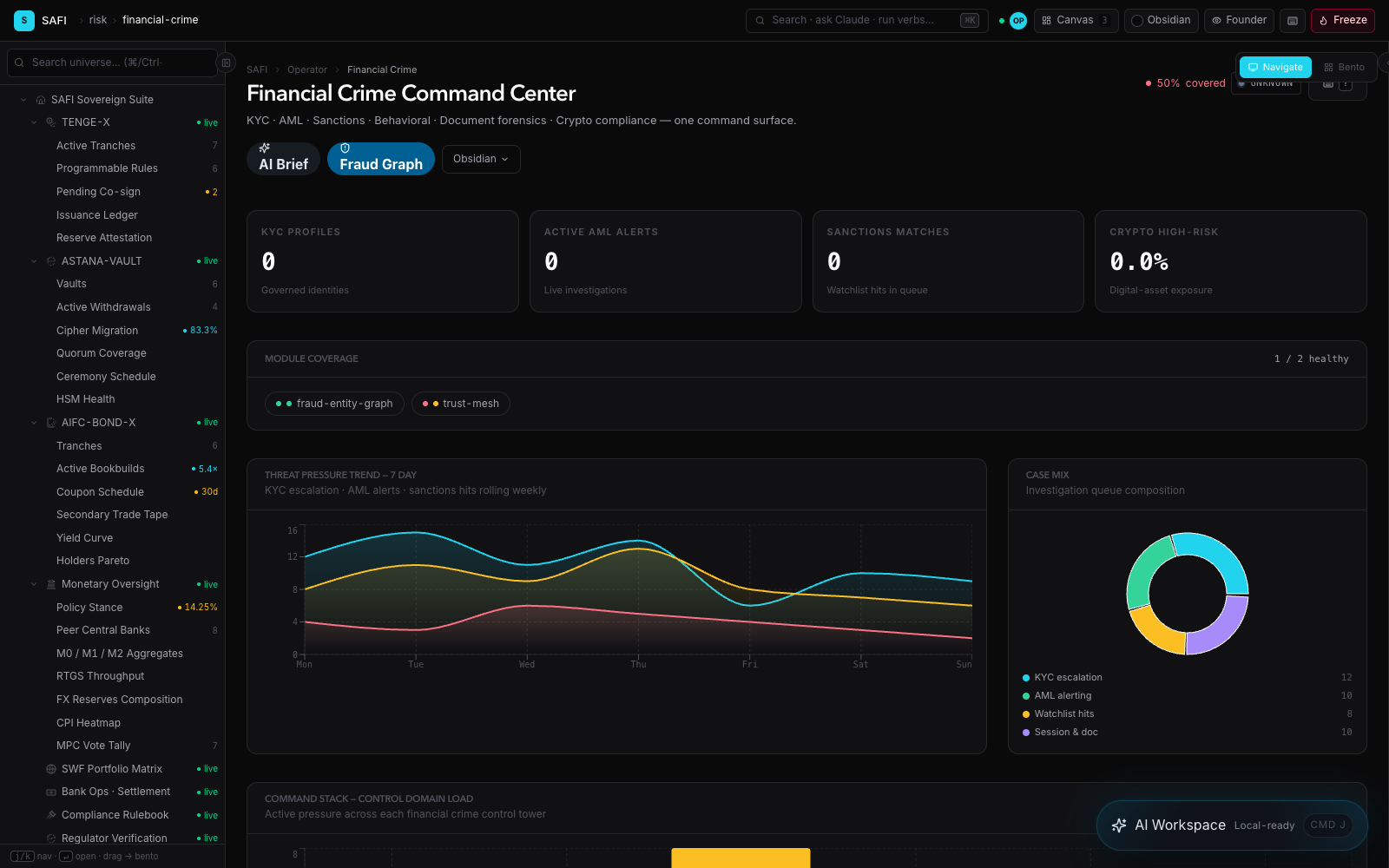
Risk & Compliance
KYC, AML, sanctions, Travel Rule, eligibility, residency, market-integrity, and disclosure workflow hooks.
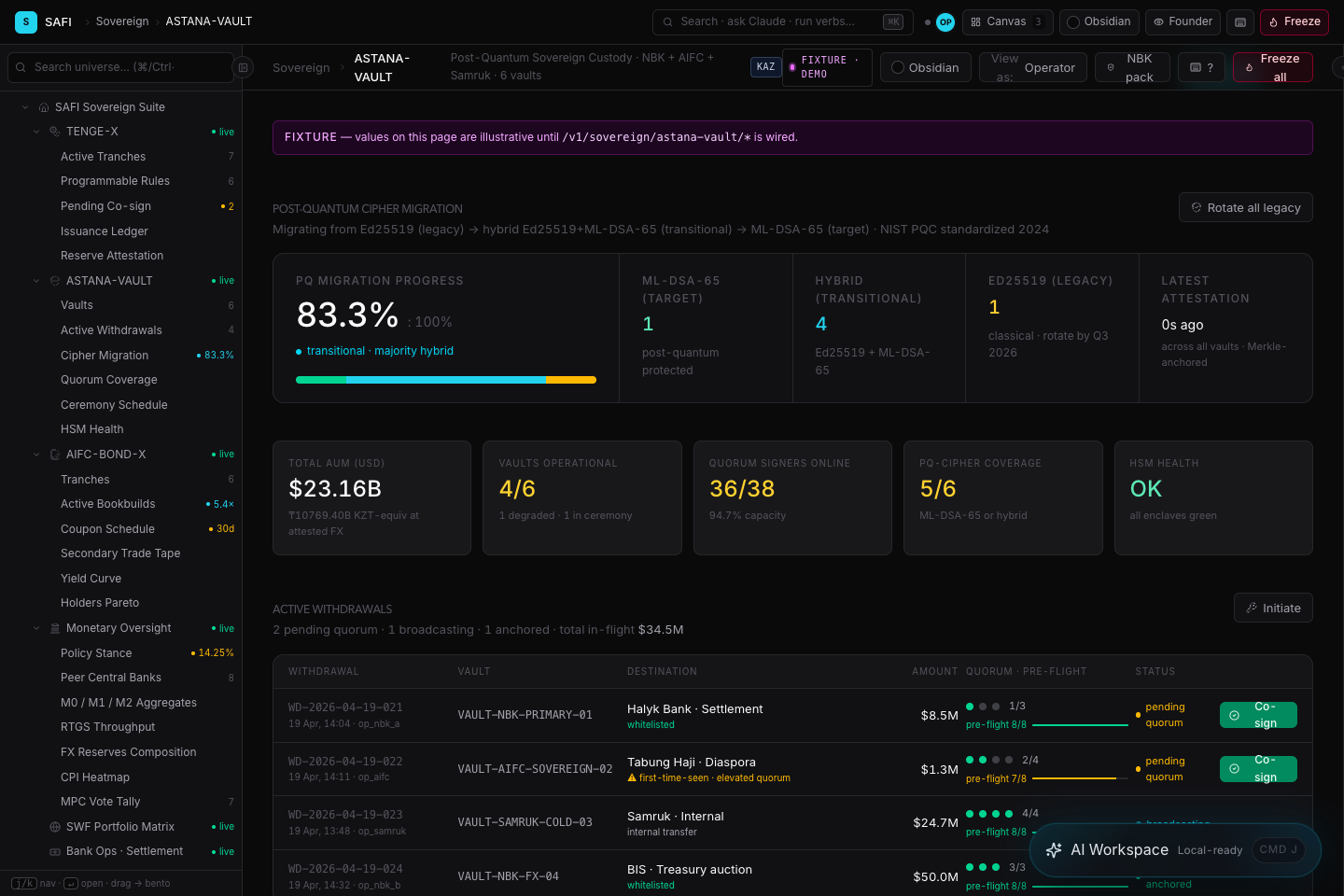
Security Posture
Hybrid post-quantum migration design, signer posture, key ceremonies, dual control, and HSM/custody workstreams.
Diligence Gates
Legal opinions, Sharia-board review where applicable, audit evidence, insurance, regulator/sandbox/no-objection evidence, and licensed partner coverage.
Product surfaces
Architecture should be shown through actual operating screens.
These SAFI screens make the trust spine concrete: verifier evidence, custody control, capital-markets lifecycle workflow, policy-bound money movement, and financial-crime review surfaces.
Capability map
Every SAFI module should map to a buyer workflow and a diligence artifact.
This table is intentionally practical. It lets investors, counsel, technical reviewers, and operating partners see where SAFI creates evidence, where the demo surface sits, and which gate must be cleared before a live regulated product.
Public claim boundary
The public page should show power without exposing secrets.
SAFI is an evidence-native operating layer for tokenized real assets, Islamic-finance workflows, programmable money, custody controls, compliance evidence, remittance corridors, and institutional trading workflows.
Selected screenshots, representative proof bundles, verifier outputs, control workflows, claims register, security posture materials, and partner-scoped implementation plans.
Patent filing details, source-code mechanics, cryptographic internals, undisclosed integrations, private partner discussions, live regulatory status, and transaction-specific legal opinions.
Verifier scope
The verifier should prove specific facts, not broad marketing claims.
For public investor materials, the strongest claim is precise: a reviewer can inspect selected artifacts and determine whether they match the signed evidence package. That does not imply regulatory approval, live custody authorization, or a securities offering.
Boundary discipline
Architecture credibility increases when the gates are visible.
SAFI can support technical demos and controlled pilots. Live regulated launch for a named jurisdiction or product still depends on the appropriate legal, custody, audit, insurance, Sharia, and partner approvals.
Security and sovereignty posture
Long-duration infrastructure finance needs controls that can survive audits, policy shifts, and cryptographic migration.
SAFI should be described as designed for rigorous control environments, subject to partner scope, independent audit, accreditation, jurisdictional review, and implementation evidence. No certification is claimed by this public page.
Post-quantum migration posture
Hybrid-signing and verifier workflows can support migration planning for long-lived real-asset instruments, subject to implementation review and external audit.
HSM and key-ceremony workstreams
Vault-state, quorum, signer posture, segregation evidence, and key-ceremony records are treated as diligence artifacts before live-value operation.
High-assurance design references
Architecture can be mapped against FIPS 140-3 L3+, CNSA 2.0, NIAP Common Criteria, STIG hardening, and data-residency requirements where the partner mandate requires it.
Audit before assertion
CMMC, government cloud, TEMPEST, or sovereign assurance claims should remain private targets until supported by documented scope, assessor evidence, and counsel-approved wording.
